Phishing Just Got Smarter.
We are officially in the era of Industrialized Phishing.
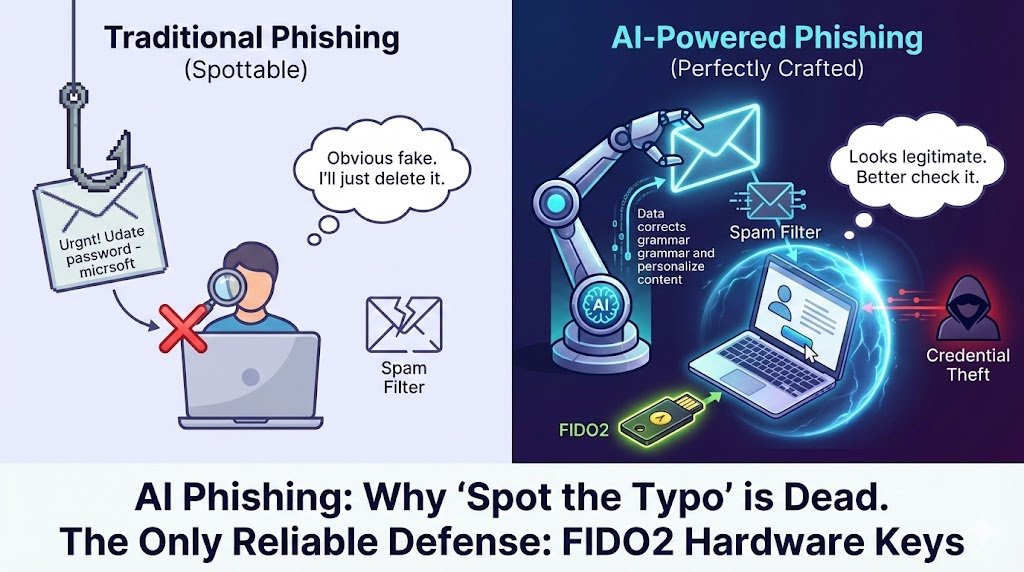
If your security awareness training is still telling employees to "look for bad grammar" or "suspicious sender addresses," you might be fighting a 2020 battle in 2026.
Here is the reality of the threat landscape this month:
The New Players: InboxPrime AI & BlackForce
Two new phishing kits—InboxPrime AI and BlackForce—have been dominating the headlines this December. These aren't just "fake login pages." They are sophisticated software platforms that anyone can buy.The Innovation (Why it’s scary)
The barrier to entry has collapsed.- Perfect English: Attackers are using LLMs (like the ones we use for work) to auto-generate perfectly written, context-aware emails. No more "Dear Customer" or broken sentences.
- Real-Time Adaptation: Tools like InboxPrime AI can reportedly analyze spam filters in real-time and adjust the email content before sending it to ensure it lands in the Primary Inbox, not Spam.
The Bypass: Man-in-the-Browser
This is the most critical part to understand. Modern kits like BlackForce use "Man-in-the-Browser" (MitB) or "Adversary-in-the-Middle" tactics.How it works (Simply):
- You click a link and see a perfect replica of your login page.
- You type your password and MFA code.
- The attacker’s server acts as a "bridge," instantly passing your real code to the real website.
- Result: You get logged in, but the attacker also gets a session token. They bypassed your MFA without you ever knowing.
The Defense: What Actually Works?
We need to be honest with our users: Human detection is failing.- Stop: Relying solely on "spot the typo" training.
- Start: Moving to FIDO2 / Hardware Security Keys (like YubiKeys). These are cryptographically bound to the domain, meaning they literally cannot be phished by a fake site, no matter how real it looks.
0 Comments
No comments yet. Be the first to comment!
Leave a Comment